Your agent can reach Git, a ticketing system, and the data lake in seconds. A weak MCP setup can turn that convenience into lateral movement at machine speed.
That’s why an MCP security checklist matters. Model Context Protocol gives AI clients a standard way to call tools and data sources, often over JSON-RPC, but it doesn’t create safe defaults. For enterprise teams, the job is to limit what an agent can do, what data it can pull, and what you can prove later.
Why MCP changes the enterprise trust boundary
As of April 2026, MCP has moved well beyond demos because it cuts custom integration work. Yet the same standard interface also widens the trust edge. A model can discover tools, choose methods, and pass arguments fast. If the tool map is loose, the model gets too much room to improvise.
A simple way to frame risk is by layer:
| Layer | What usually goes wrong | First control to apply |
|---|---|---|
| Protocol level | Weak client-server auth, weak transport protection, unclear server trust | TLS 1.3, strong token or mutual auth, trusted server registry |
| Implementation level | Over-permissioned tools, unsafe agent-to-tool calls, parameter abuse | Strict allowlists, typed schemas, read-only defaults, sandboxing |
| Organizational level | Shadow servers, poor vendor review, thin logs, no owner | Server inventory, approval gates, audit retention, access reviews |
Most failures sit between these layers. The protocol may support auth, yet your server might still accept a broad shared token. A tool may look harmless, but a “sync” method can still write, delete, or trigger downstream jobs.
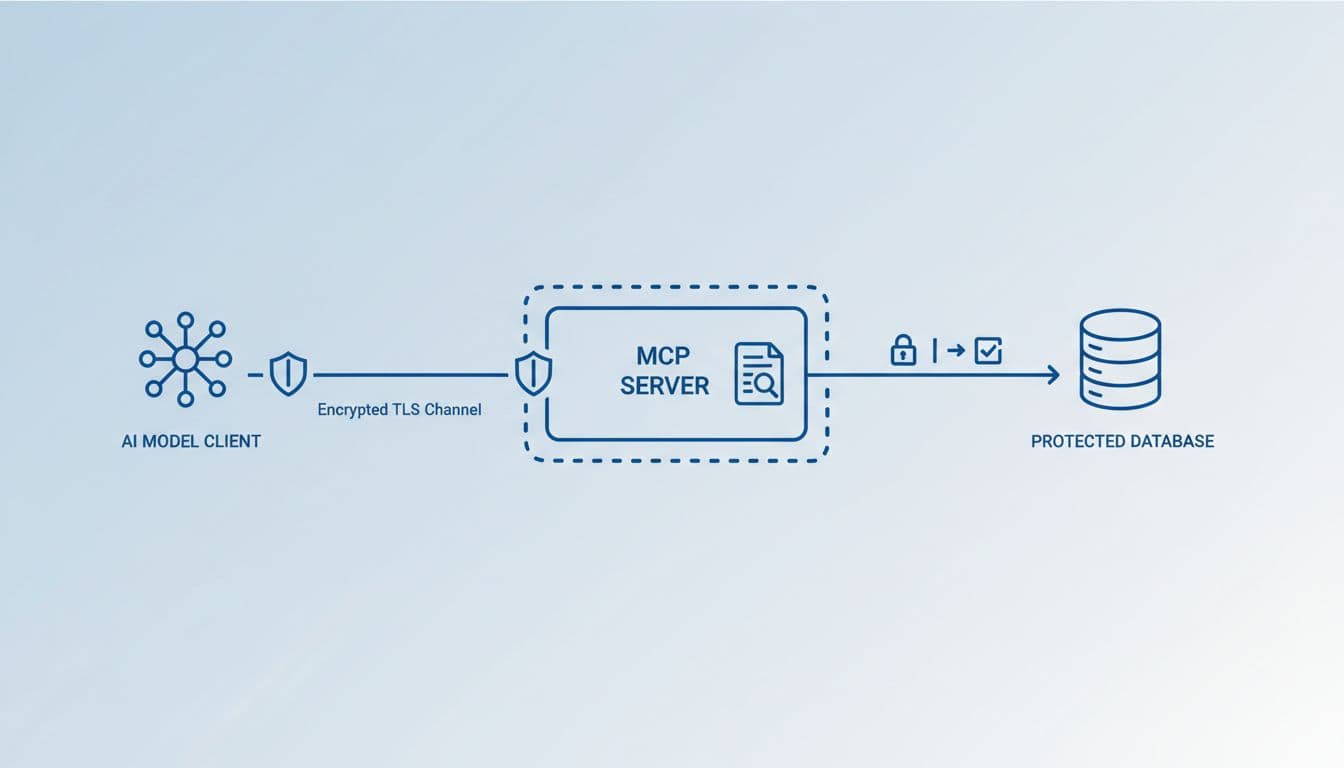
Standards and deployment patterns are still moving. So, treat MCP as a transport and orchestration layer, not a security boundary by itself. The official MCP security best practices and the OWASP MCP Security Cheat Sheet both push the same theme: least privilege, explicit validation, and strong audit trails.
MCP is a protocol, not a permission model. You still have to define who may call what, with which data, and under which conditions.
A practical MCP security checklist for enterprise AI teams
The best checklist starts small and stays boring. If a server exposes ten methods when two will do, the attack surface has already grown.
- Start with read-only tools. Add write actions only after a review of business impact, rollback steps, and abuse cases.
- Bind each MCP server to a narrow service identity. Avoid shared API keys, hardcoded secrets, and long-lived tokens.
- Validate every tool argument against a schema. Reject free-form commands, unsafe file paths, hidden shell execution, and silent retries.
- Put high-risk actions behind approval gates. Deletes, payments, user provisioning, and production changes should not run from model output alone.
- Isolate servers in containers or sandboxes. Also restrict network egress so a compromised server can’t wander into unrelated systems.
- Log the full chain of custody. Capture the human user, agent session, tool chosen, arguments hash, result, and approval state.
Common failure modes are easy to miss in testing. One team gives an agent a repo tool with broad write scope because it “might need to fix code.” Another lets the model pass raw text into a shell-backed tool, which turns a vague request into unsafe command execution. Sensitive data leakage shows up too, often through oversized context windows, verbose tool results, or logs that store secrets in plain text.
Weak authentication between clients and servers is another blind spot. If tokens are broad, shared, or poorly rotated, one stolen secret can unlock several servers at once. In practice, the safer pattern is narrow identity, short-lived credentials, and explicit scoping per tool or tenant.
Third-party MCP servers, governance, and auditability
Third-party MCP servers deserve the same review you’d give a new SaaS app plus a new privileged integration. They may be well built, but they also sit between your agent and your systems of record. That means supply chain risk, patch risk, and trust drift over time.
Before you approve one, ask where it runs, how it authenticates, what it stores, and how fast it patches. Also ask whether it supports scoped access, customer-visible logs, and clear method boundaries. This enterprise analysis of MCP server exposure is useful because it frames MCP as a trust-model change, not just another plugin format.
Auditability often breaks first. Many teams can see the agent prompt, but not the downstream tool call. Others can see the API call, but not which human or policy approved it. That gap matters during an incident. If you can’t tie user intent to agent action and server response, your logs tell half the story.
Build organizational controls around that gap. Keep a live inventory of approved MCP servers. Assign an owner to each one. Run periodic access reviews. Route high-risk servers through a common gateway or broker if you can. Red-team prompt-to-tool abuse, not only the server code. Also test for noisy but realistic failures, such as an agent selecting the wrong tool, retrying a side-effecting action, or pulling sensitive data into a chat transcript.
A useful checklist doesn’t promise safety. It reduces surprise, narrows permissions, and gives responders evidence when something goes wrong.
The strongest signal of a mature deployment is not how many tools your agents can call. It’s how few they can call, how tightly those calls are scoped, and how clearly your team can reconstruct every action afterward.

