If your enterprise encrypts traffic today, assume someone may record it for later. That’s the core of the “harvest now, decrypt later” problem, and TLS is right in the blast radius.
A post-quantum TLS migration in 2026 isn’t a single switch. It’s a controlled change across dozens of termination points, thousands of clients, and multiple PKI paths. The winners won’t be the teams with the boldest roadmap, they’ll be the teams with the cleanest inventory, the most crypto agility, and the best observability.
Executive summary for security and infrastructure leaders
NIST published its first post-quantum cryptography standards in 2024 (FIPS 203 for ML-KEM key establishment, plus FIPS 204 and FIPS 205 for signatures). In early 2026, enterprise guidance is consistent: start integrating now, because full migration takes years and dependencies move slowly.
For TLS, most enterprises should plan around hybrid handshakes first (classical ECDHE plus ML-KEM, often referred to as X25519 plus Kyber/ML-KEM). That reduces long-term exposure while keeping compatibility.
What you can do now in 2026:
- Inventory every TLS endpoint and crypto library, including hidden mTLS.
- Add crypto agility (policy-driven algorithm selection, fast rollback).
- Pilot hybrid PQTLS on low-risk paths with real traffic.
What still depends on standards and library support:
- Mature, widely compatible PQTLS defaults across browsers, mobile stacks, middleboxes, and enterprise runtimes.
- Scalable post-quantum certificate chains and signing support across your internal and public PKI.
For governance and audit readiness, align your work with a time-boxed program, for example ISACA’s 12-month PQC playbook.
Where PQTLS changes apply in real enterprise stacks
Start by drawing the map of where TLS terminates and where keys live. In large environments, it’s rarely “the web server.” It’s your CDN edge, load balancers, ingress controllers, API gateways, service mesh sidecars, and outbound proxies. Each one may run a different TLS library and support set.
PQTLS changes hit three areas:
First, handshake mechanics change. Hybrid key exchange increases handshake payload size and CPU cost. That can stress busy edges and chatty east-west mTLS.
Second, certificates and chains change. Post-quantum signatures and larger artifacts affect handshake size, caching, OCSP behavior, and even MTU edge cases. The practical impact is often manageable, but you need to plan it, see how PQC affects certificates and handshake performance.
Third, operational control becomes the real risk boundary. If you can’t quickly change algorithms per endpoint and per client class, you’ll either break users or freeze progress.
A phased post-quantum TLS migration plan for 2026 (with time ranges)
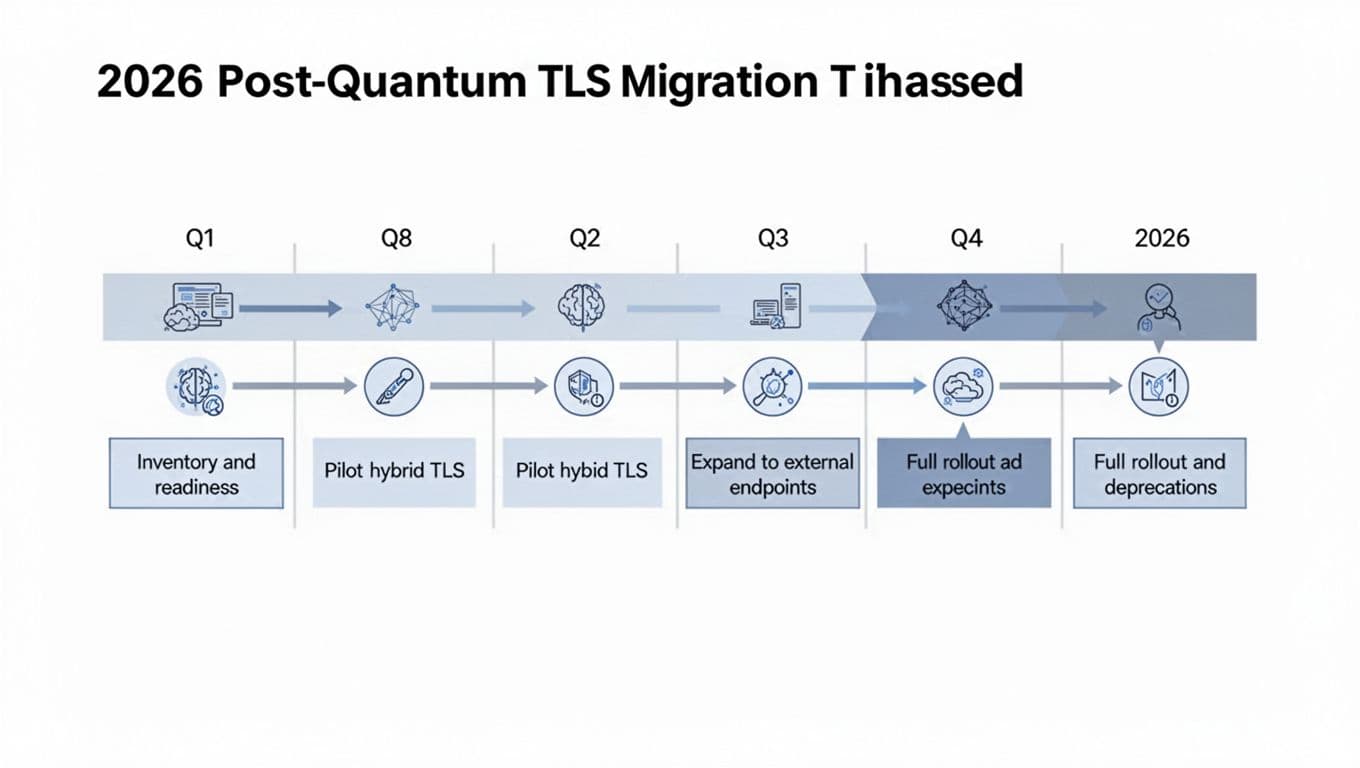
Use this table as a default plan, then adjust by risk and client diversity.
| Phase (2026) | Estimated time | What you change | Exit criteria |
|---|---|---|---|
| Inventory and readiness | 4 to 8 weeks | TLS termination catalog, crypto SBOM, cert paths, HSM capacity, logging gaps | 95% endpoint coverage, per-endpoint TLS policy control, baseline KPIs |
| Pilot hybrid TLS | 6 to 10 weeks | Hybrid KEX on selected internal mTLS and one external low-risk hostname | Handshake failures stable, latency and CPU within guardrails |
| Expand to external endpoints | 8 to 12 weeks | Broader edge rollout by client allowlist, plus API gateway and ingress tiers | Canary proves stable across key client sets, support tickets don’t spike |
| Rollout and deprecations prep | 4 to 8 weeks | Standardize configs, automate cert rotation, document deprecation windows | Go/No-Go met, rollback tested, comms and contracts updated |
A useful reality check in 2026: national bodies expect multi-year migration timelines, so treat 2026 as the year you build repeatable controls, not the year you “finish.” The NCSC PQC migration timeline guidance is a good anchor when setting leadership expectations.
Compatibility matrix to test before enabling hybrid PQTLS
Hybrid PQTLS will fail first at the edges, older clients, or TLS-inspecting boxes. Test with representative devices and runtime versions you actually see in logs, then add worst-case legacy.
| Client or environment | Examples to include | Test priority | Common failure modes to watch |
|---|---|---|---|
| Browsers | Chrome, Edge, Firefox, Safari (current and n-1) | High | Middlebox intolerance, handshake size limits |
| Mobile OS | iOS (current and n-1), Android (current and top 2 active LTS baselines) | High | TLS stack gaps in embedded WebViews |
| Java runtimes | Java 8, 11, 17, 21 | High | Old JSSE providers, pinned cipher suites |
| .NET | .NET 6, .NET 8 | Medium | Handler differences, proxy behavior |
| Go services | Go (current and n-1) | Medium | Library build flags, FIPS mode constraints |
| Linux tooling | curl, OpenSSL, system trust stores | Medium | CA bundle issues, SNI and ALPN quirks |
| Network middleboxes | TLS inspection, DLP proxies, WAFs | High | Breakage on unknown groups or larger handshakes |
| Legacy and embedded | IoT gateways, POS, old printers | High | Hard-coded TLS, no update path |
Treat this matrix as a living artifact. Every new rollout wave should add “top talkers” and “top error sources” from your telemetry.
Risk register (top risks and mitigations)
| Risk | Why it matters in 2026 | Mitigation that works at scale |
|---|---|---|
| Client incompatibility | Hybrid PQTLS isn’t uniformly supported | Client allowlists, canaries, quick policy rollback per hostname |
| Performance regression | CPU and bandwidth rise at busy edges | Load tests, capacity buffers, session resumption tuning |
| Middlebox breakage | Inspection devices can drop unknown handshakes | Bypass policies, staged rollout, vendor escalation path |
| PKI and cert lifecycle strain | New algorithms change issuance and rotation patterns | Automate issuance, shorten blast radius, validate HSM throughput |
| Incomplete crypto inventory | Shadow TLS endpoints keep old algorithms alive | Traffic discovery, config scanning, ownership tags per endpoint |
If you can’t answer “which library and policy serves this hostname,” you don’t have crypto agility, you have hope.
KPIs, rollout gates, and rollback controls
Track KPIs per tier (CDN, LB, gateway, mesh) and per client cohort (browser, mobile, partner API, legacy). Alert on deltas, not raw values.
| KPI | How to measure | What “good” looks like |
|---|---|---|
| TLS handshake failure rate | Errors by reason code, client type, tier | No sustained increase after enabling hybrid |
| Median and 95p TLS handshake latency | Real user and synthetic probes | Within agreed SLO deltas for each endpoint class |
| Edge CPU and memory | Per-node resource metrics during peak | Headroom preserved, no eviction or throttling events |
| Cert issuance and rotation success | Issuance time, failures, retry counts | Predictable issuance, rotations complete inside window |
| Rollback time | Time to revert policy and confirm recovery | Minutes, not hours, with clear verification signals |
Go/No-Go checklist (use before each expansion wave)
- Endpoint inventory coverage and ownership are current.
- Hybrid policy can be enabled per hostname, per client cohort.
- Canary results include peak traffic windows and real client mixes.
- Support and incident teams have updated runbooks and dashboards.
- Partner and B2B endpoints have notified clients and tested.
- Rollback has been executed in a rehearsal and recorded.
Rollback triggers (stop the wave, revert, then investigate)
- Handshake failures exceed your threshold for more than 10 minutes.
- 95p handshake latency breaches SLO in two regions or more.
- Edge CPU saturation causes cascading timeouts or autoscale churn.
- Certificate issuance failures block rotation or emergency re-key.
- A middlebox or inspection tier shows systematic drops on hybrid.
Conclusion
Quantum-safe TLS won’t arrive as a tidy deadline. It will arrive as a long series of small changes, and attackers will benefit from every year you wait.
A disciplined post-quantum TLS migration in 2026 starts with inventory and agility, then grows through pilots, compatibility testing, and measured expansion. Build the controls now, so later algorithm shifts feel routine, not risky.

